What Is Employee Monitoring Software?
The first tool for monitoring employees appeared as long ago as in the year 1888. The progress is pacing forward, and today’s statistics shows that one out of three companies is engaged in employee computer monitoring, from viewing employees’ e-mails and installing time-tracker systems to total data traffic control.
This is not because of some paranoia an employer may suffer. There is a good reason for an employer to monitor the employees.
So far, 89% of companies worldwide have faced insider information leaks. In 69% of the cases these leaks caused significant losses for the companies.
Even a secretary chatting on FB instead of receiving calls, or, let’s say, a manager carried away with MMORPG during work hours instead of handling customers, are responsible for the company’s loss of 1000 $ per month on average.
There are some other nuances to name and to blame. Every other company has got some underminer who is building up the atmosphere of frustration in the team and boosts personnel’s distrust in the management. As a result, the company faces productivity downfall which could have been avoided had the trouble-maker been revealed in due time (how to troubleshoot these trouble-makers is yet another question).
With drastically growing competition in all business sectors, corporate CEOs are facing tough times. To make the company reach the leadership positions, every single element of working process should be optimized to its best. Besides, it should be mentioned that in the majority of the cases employee activity monitoring does not mean putting all the personnel under total surveillance. It usually implies checking on the employees who are already under question. If not monitoring them, a company may suffer painful data leaks, just like in the recent Tesla management data leak case.

Is It Legal to Monitor Employees Computers?
We are all well aware that the law guarantees the personal privacy of an individual. This, in theory, means that no one has the right to spy on our correspondence. But if we use messengers while performing work duties, that’s a whole different story.
In fact, the employers actually lease the personal time of their employees. Thus, their personal time is turned into working time, changing its status and losing immunity. As a consequence, the relevant constitutional article does not apply here. Moreover, corporate network traffic does not belong to an employee as well. Therefore, it does not matter whether they use a common messenger or a corporate one, as everything that flows through corporate network traffic is automatically considered the company’s property.
That is why employee computer monitoring is totally in accordance with the letter of the law. As for ethical and moral aspect of this subject, we clearly state that our software is solely intended for corporate purposes and for enhancing business performance, and shall never be used for voyeuristic or any other pervert intentions.
It is obvious that there may be a very fine line between the intended purpose and wrongful exploitation of such mighty software. So, it should always be remembered that real violation of individual privacy (for instance, monitoring the computers of freelancers during their off-duty time) is subject to criminal liability and may bring serious troubles. But if your company shows clear evidence of productivity loss, something has to be done. Luckily, numerous solutions for remote computer monitoring are available on the market.
Let’s mention that it is important to avoid going to extremes. Too much obsessive monitoring increases stress level in employees and may even motivate them to look for another job. Besides, creativity can’t be controlled with a time-tracker, neither can be monitored the thought process.
Employee monitoring software should not be considered absolute evil for the employees themselves. In our own experience, we have seen many cases when employee monitoring software was actually used for the benefit of the employees.
For instance, the most productive employees received recognition on the grounds of employee performance evaluation report. In some other case online monitor activity recording helped not only to spot the insider, but at the same time to clear well-meaning workers of any suspicion. This feature was also a great help in building efficient cooperation between corporate departments. To sum up, even if someone could not recall their password at some important resource, keylogger was there to help.
Different Types of Employee Monitoring Software
Remote access software
At the onset of monitoring software market, programs like TeamViewer were used for remote access to the computers of the employees, including outsourcers. Such software is not specifically customized for spying, but nevertheless it can be used for basic monitoring functions.
For example, the abovementioned TeamViewer provides for employee screen mirroring by connecting two or more computers located no matter how far away one from another.
Radmin is another program with similar basic monitoring functions which was initially developed for remote technical support. Ammyy Admin, Supremo Remote Desktop, mRemoteNG, TightVNC, Remote Utilities can also be added to the list of such software. There is an only nuance that these programs can’t operate in stealth mode, so an employee is surely aware that the eye of Sauron… sorry, the boss’s eye is watching relentlessly all the time. Thus, it can’t be attributed to hidden monitoring of a remote computer.
Spyware for hidden computer monitoring
Now let’s move on to hidden computer monitoring. It’s obvious that when employees have no idea they are being watched, they are behaving in their natural way, doing what they are used to do. That’s why spyware operating in stealth mode is way more efficient.
The most primitive hidden computer monitoring spyware is a keylogger. According to our information, some old-school sysadmins are still using them in small companies. Keyloggers do not provide for employee computer monitoring or remote control, but they suggest something not less effective.
Keyloggers (also widely known as keyboard capturers) are spyware programs that record the keys struck on a keyboard. Data of all the keys pressed during the working day is then kept in a special logfile available for access of authorized persons. Sysadmins may put such hidden monitoring program into operating system process, or disguise it as running system task. The following top keyloggers are particularly worth mentioning: Ardamax Keylogger, Actual Spy, Spyrix Personal Monitor, Spytech SpyAgent, Refog Personal Monitor, All In One Keylogger, Elite Keylogger, Spytector.
Videologgers (not to be confused with videobloggers) operate the same way as keyloggers, but instead of logging keys pressed on the keyboard, they record screen activities making either screenshots or recording videos of monitor actions. Such programs may be activated with different frequency following target actions. They may also run in hidden mode and then transmit logfiles of their spying activity to the boss’s computer.
Computer spyware goes even further and may be actually considered as a tool for modern James Bond. According to its modification, spyware can collect almost any type of data. It allows you not only to obtain keylogging data or monitor screenshots, but also to get reports on visited websites, to intercept clipboard contents, e-mails, and files sent for printing or to removable USB drive. NeoSpy, Real Spy Monitor, Spy Go are the examples of the most popular computer spyware.
Spyware programs are widely used in different spheres. Apart from employee computer monitoring in an office, they are also used for private purposes such as spying on adultering spouses, or for parental control on the kids’ computers, etc. Please note that these programs and their elements can be used by hackers and fraudsters for malicious purposes, including stealing logins and passwords and other types of personal data.
The major drawback of all abovementioned programs is that they can’t operate in multi-user mode, therefore they do not meet the needs of medium and large companies.

How Does Employee Computer Monitoring Software Work?
Such programs are more than just remote control software. Instead, they provide for total monitoring of computers of any of your managers, or a secretary, or a designer, or even information security administrator. These solutions are really diverse and multi-faceted, so it’s better to have a closer look at them using some illustrative example.
To begin with, Kickidler is our exclusive proprietary solution developed on the grounds of long-term experience of our foreign colleagues. It is worldwide unique for a number of its functions. It is compatible with Windows, Mac, Linux, and it may run in either open or hidden mode.
Kickidler’s modus operandi is simple: Server program is installed onto the main computer, Viewer program is installed onto the computers of the executives authorized for employees monitoring, Grabber program is installed onto the computers of the employees to be monitored. There may be as many Grabbers, Viewers and even Servers as you need. If required, the client can store the Server in their own cloud service.

Grabber may run in both open or hidden mode. If necessary, it may be turned into completely invisible mode for a user.
There are two versions of Kickidler employee monitoring software - Kickidler Time Tracking and Kickidler Employee Monitoring.
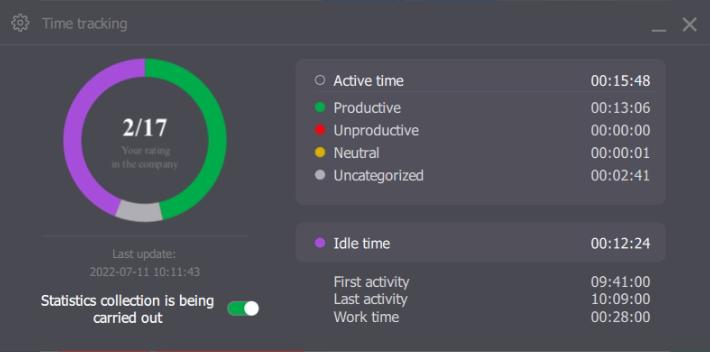
Kickidler TT is, essentially, a time tracker that ensures more gentle employee monitoring through its analytics, reports on working time, and self-monitoring that’s enabled by Autokick’s functionality. You don’t need to install the Viewer to use this version of the software.
Kickidler EM includes features of Kickidler TT and additionally offers visual monitoring tools, such as online screen monitoring, screen video recording, and keystroke logging (keylogger). Kickidler EM allows managers to have full supervision of the PCs of their subordinates. It is impossible to cheat this version of the software thanks to its visual monitoring features.
Kickidler is a mighty source of solutions. It would be difficult to list them all, so let’s dwell on the key ones.
In 2023, Kickidler's software developers introduced two new features:
- An "Activity History" report that provides a detailed overview of an employee's entire computer activity history.
- A feature for recording incoming and outgoing audio from both phone calls and video conferencing applications.
Project & Task Monitoring Functionality
In 2024, Kickidler employee monitoring software introduced a number of new tools that allow managers to see a much broader picture in terms of project management in their company.
In addition to time tracking, you can now evaluate the quality of the work being done during the working hours, examine certain task-related details, and analyze employee productivity, not just in terms of total time they devote to work, but also in terms of the amount of time they dedicate to specific projects.
You can access statistics both big projects and their epics (large bodies of work), as well as monitor the work of each division within the company.
With the help of these tools, you are now able to set specific tasks for your employees and monitor their status, use time tracking features that collect data on working days and even whole weeks and months, get understanding of where your finances go and what tasks your employees spend their time on.
Kickidler now generates a map of tasks and activity of each employee, which will be useful for both managers to track employee performance and employees to implement self-monitoring.
A nice bonus among all the new Kickidler updates is the option of custom branding the software for your company. You will be able to add your logo or use corporate colors, thus increasing the trust of your employees.
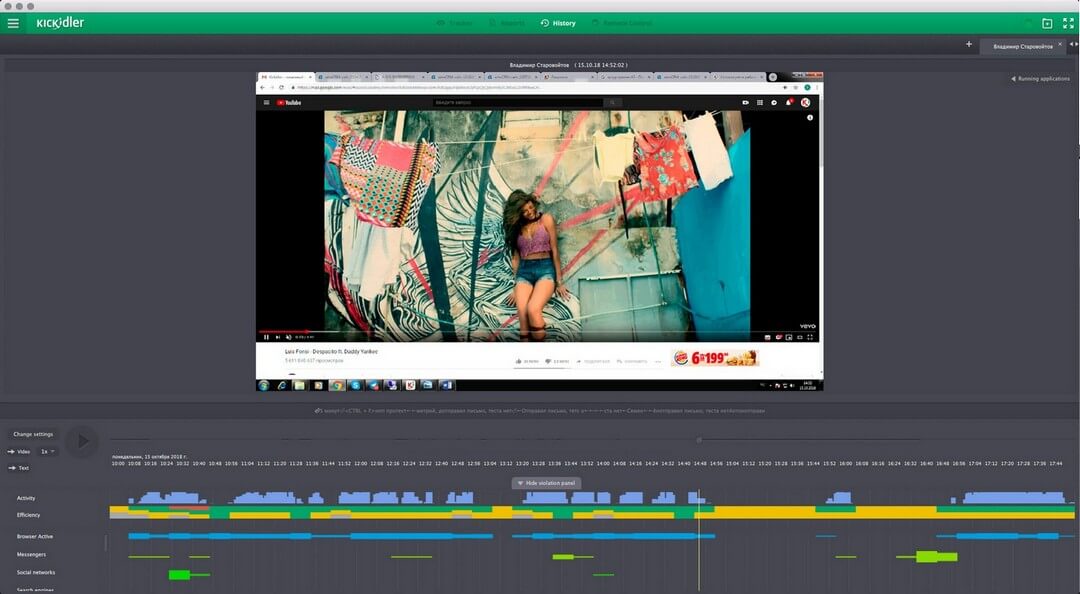
Monitor activity recording
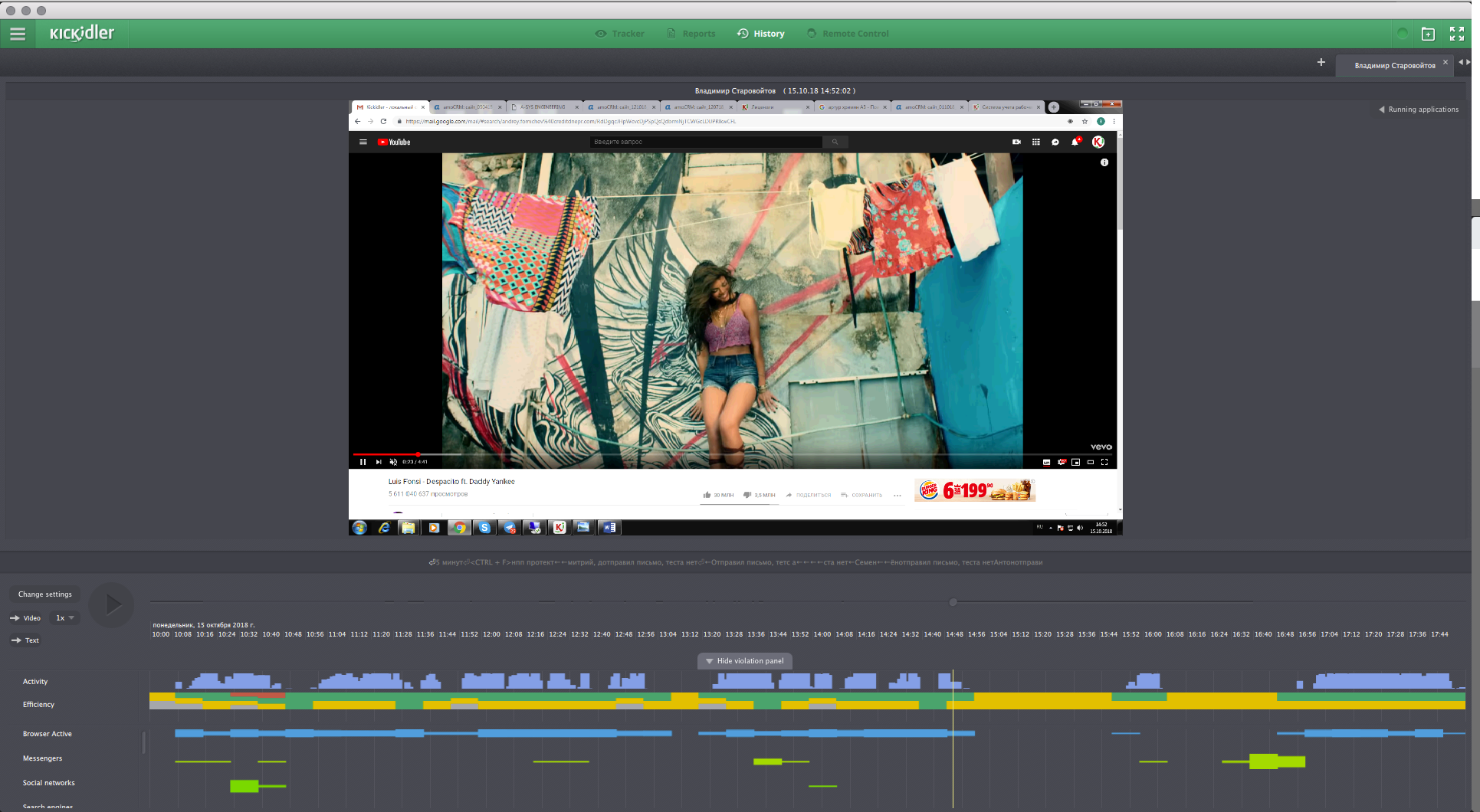
Monitor activity recording feature
As for videologging, Kickidler does not just make screenshots like other monitoring programs, but records a full-featured video of employee desktop activity with a rate of up to 30 frames per second. Viewing toolbar panel also allows to oversee the keys an employee presses on the keyboard at the same time and applications running on the computer. Monitor activity recording is carried on offline as well, when the employee’s computer has got no access to the Internet.
The Viewer allows to watch monitor activity recordings in usual mode or fast forward mode. The user can sort videos by certain apps running or certain websites visited. This feature is unique and does not have analogues worldwide. Owing to video data compression, these video files do not take much space. They may be kept as archives for many months or even years (however, by default they are only kept for 7 days, this is far enough as we have seen from our experience).
Online monitoring and control of employee activities (real-time computer monitoring)
This feature allows to oversee what an employee is busy with at the current moment – what apps are running on the computer and what websites are being visited. Real-time screen activity of the computers with Grabber installed are webcasted live via Viewer on the manager’s or CEO’s computer.
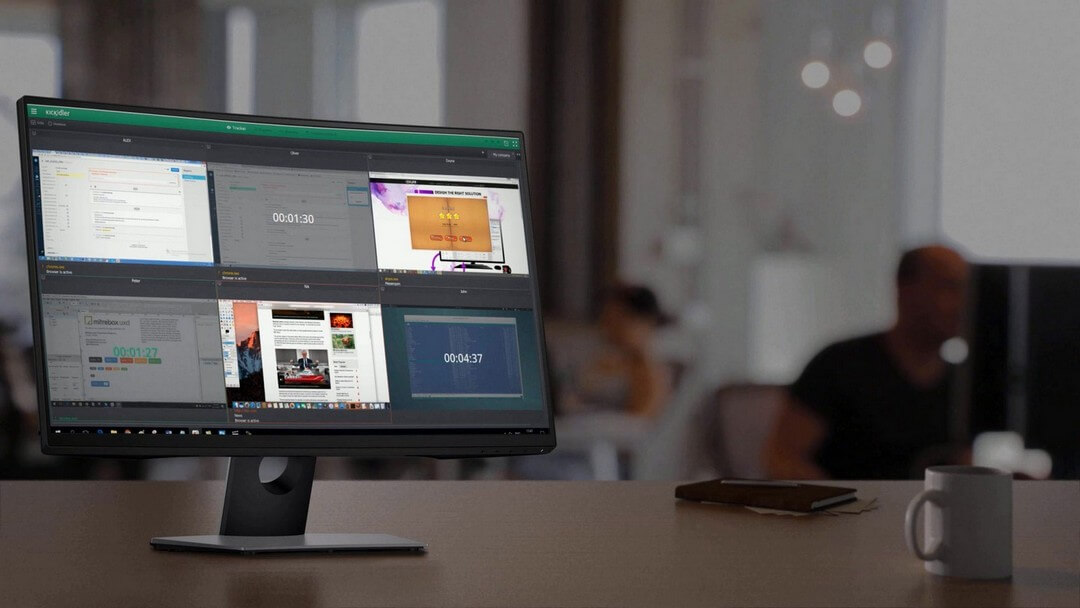
Kickidler has got a very user-friendly interface, Quad Splitter, for live webcasting of employees’ desktops. Quad Splitter allows to display on the computer screen an unlimited number of employee desktop views, although we highly recommend to divide them into smaller groups (for instance, sorting by corporate subdivisions) and then switch between them. As an alternative option, use several displays for monitoring all computers of a whole department at the same time.
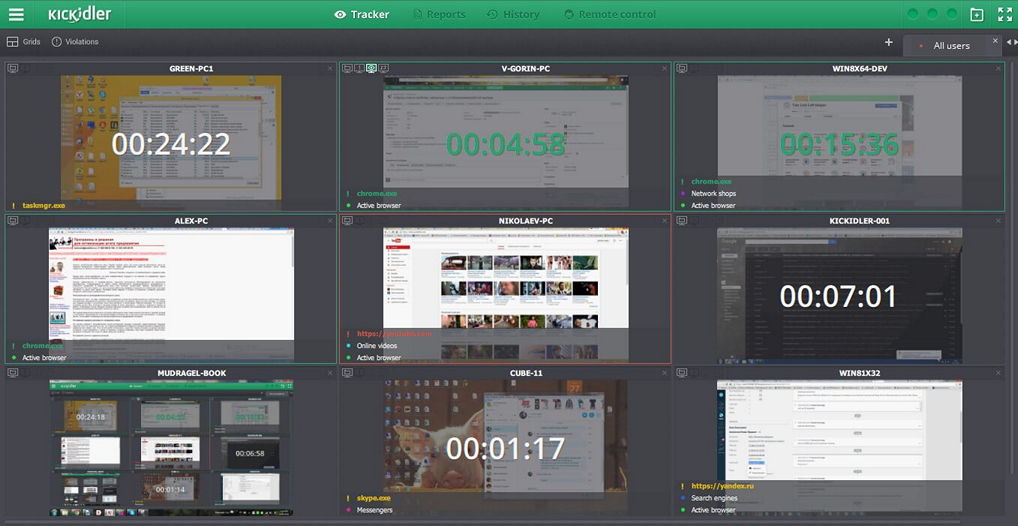
Screenshot: Quad Splitter interface
If needed, you may click on a particular quad and turn it full-screen so as to have a closer look at the activities of a certain employee.
Check this video to see how Quad Splitter works:
Time logging system (Time tracking)
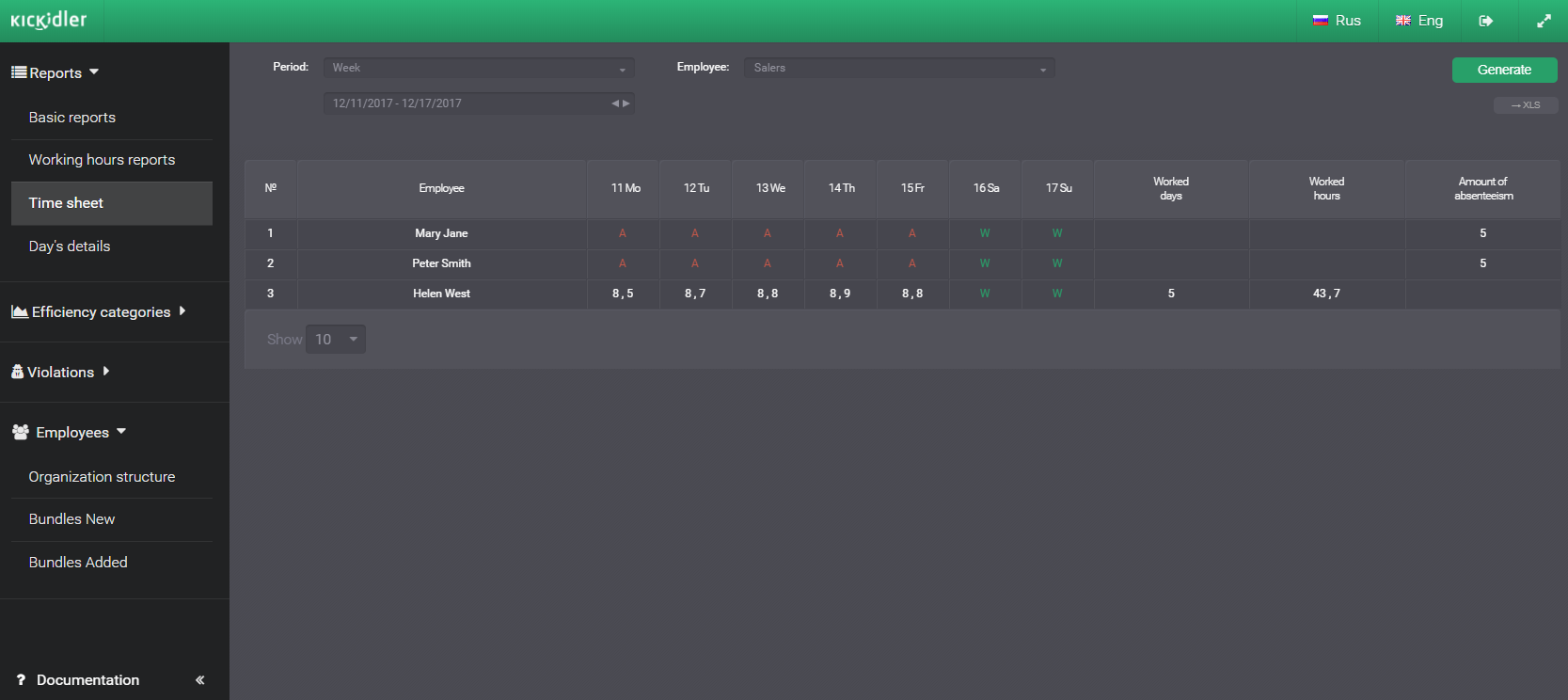
Time tracking features allow to record time of all actions of an employee on the computer – the actual time of arrival at work, time of lunch break, time of absence at the work place, etc. All these data are recorded in Time Tracking report and in the Time Sheet.
Screenshot: Time tracking report
These data are presented in the form of graphs or diagrams and can be shown in Viewer or in its web user interface, or in an e-mail set for sending at a convenient time. It is much easier than to flip through the pages of real-life time register.
Screenshot: Time Sheet
While the previous feature suits intuitive persons, this feature is designed rather for sensory types of users who want structured information which allows to have an overall view of efficiency of a certain employee or a whole department.
By the way, you don’t even have to start Viewer in order to check on the employees’ efficiency report, as it is available in Kickidler web interface as well.
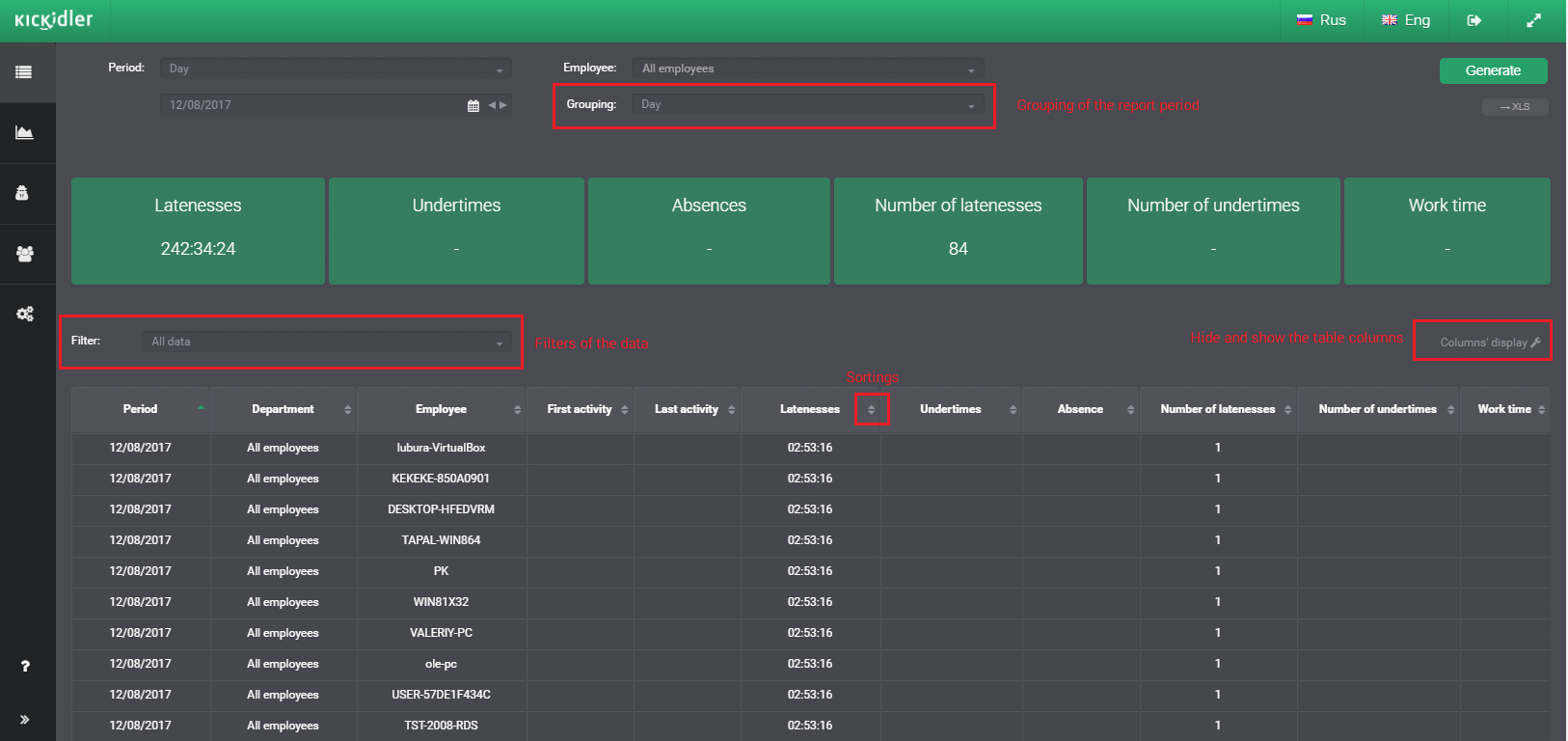
Screenshot: “Details of the day” report
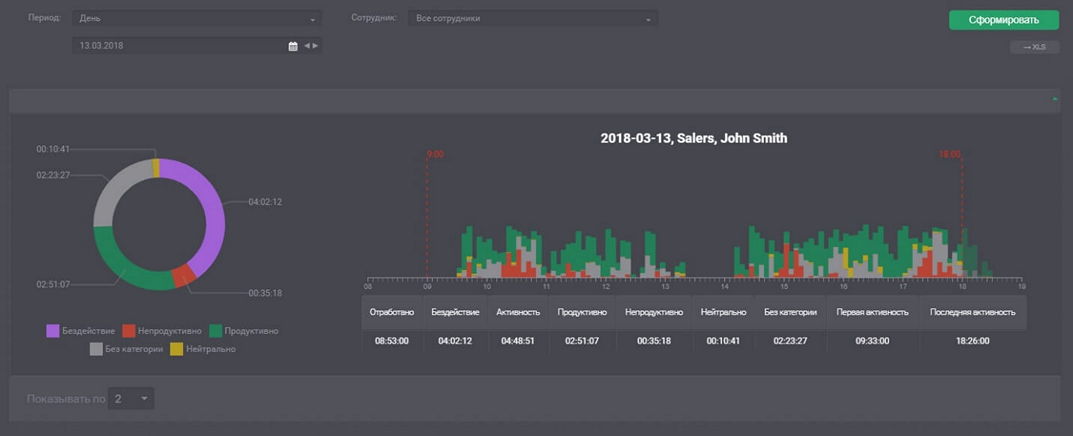
Work time efficiency report
Work time efficiency reports are presented in the form of pie charts or line charts in which productive actions, non-productive actions, and neutral actions of the employees are marked with different colors. Height of every bar of the histogram reflects the intensity of the employee’s activities at the given period of time (one bar equals 5 min). Spaces refer to the time when the user was idle. A pie chart shows the percentage of time an employee wasted on surfing social networks and the percentage time dedicated to actual work assignments.
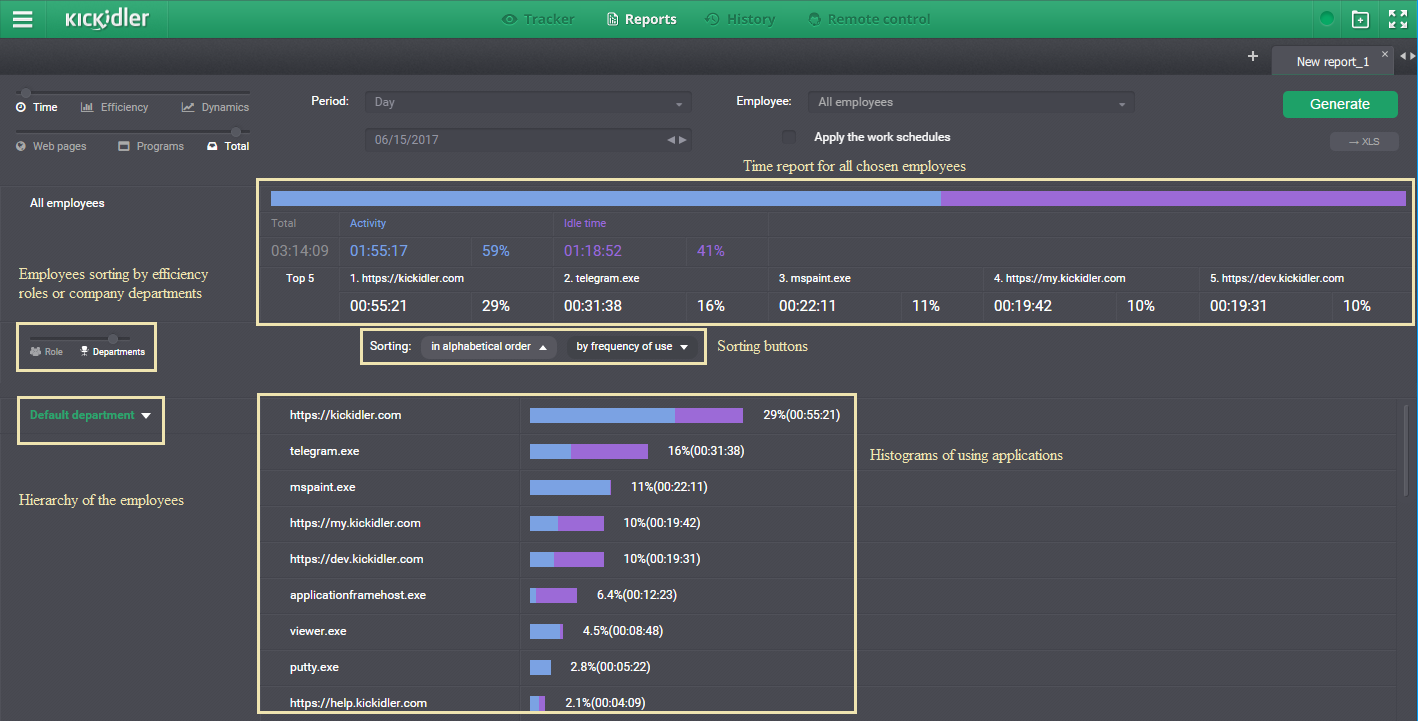
Screenshot: time tracking report in the form of a line chart
Productive activity of an employee is estimated on the basis of the time spent on the websites and applications required for performing work assignments and listed as productive web resources. For instance, Photoshop and Corel are considered productive applications for a designer, while SAP is a productive application for an accountant.
Non-productive resources are listed the same way. For example, if your employee spends half of a working day on FB, it will be recorded as non-productive activity. Provided that this employee does not work with social media marketing, of course. If a programmer is using Word, it will be also recorded as non-productive activity. Why a programmer would ever use Word? Applications and web resources are listed as Neutral if they may be used for both productive and non-productive activities. A good example of such resource is Google searching machine.
All the activities which are not marked Productive, or Non-productive, or Neutral, are recorded as Not Assessed.
Autokick – remote employee monitoring tools
Kickidler’s new features, released in 2020, have made it even more autonomous and easier for monitoring remote employees.
Automatic notifications notify employees that they are engaged in unproductive activity or that they have been working without breaks for quite some time.
Self-monitoring interface allows employees to see infographics of their own productivity that is a good motivation for them to improve their performance.
Grabber's on/off button allows employees to manage the monitoring themselves. This is necessary, for example, for remote employees that work from home PCs. When the monitoring is turned off, no statistics get collected from the computer.
Keylogging function
Using keylogging feature Kickidler records all the keystrokes on the keyboard and displays the keylogging report at the special tab of the Viewer. Search command by a keyword is available for keylogging files.
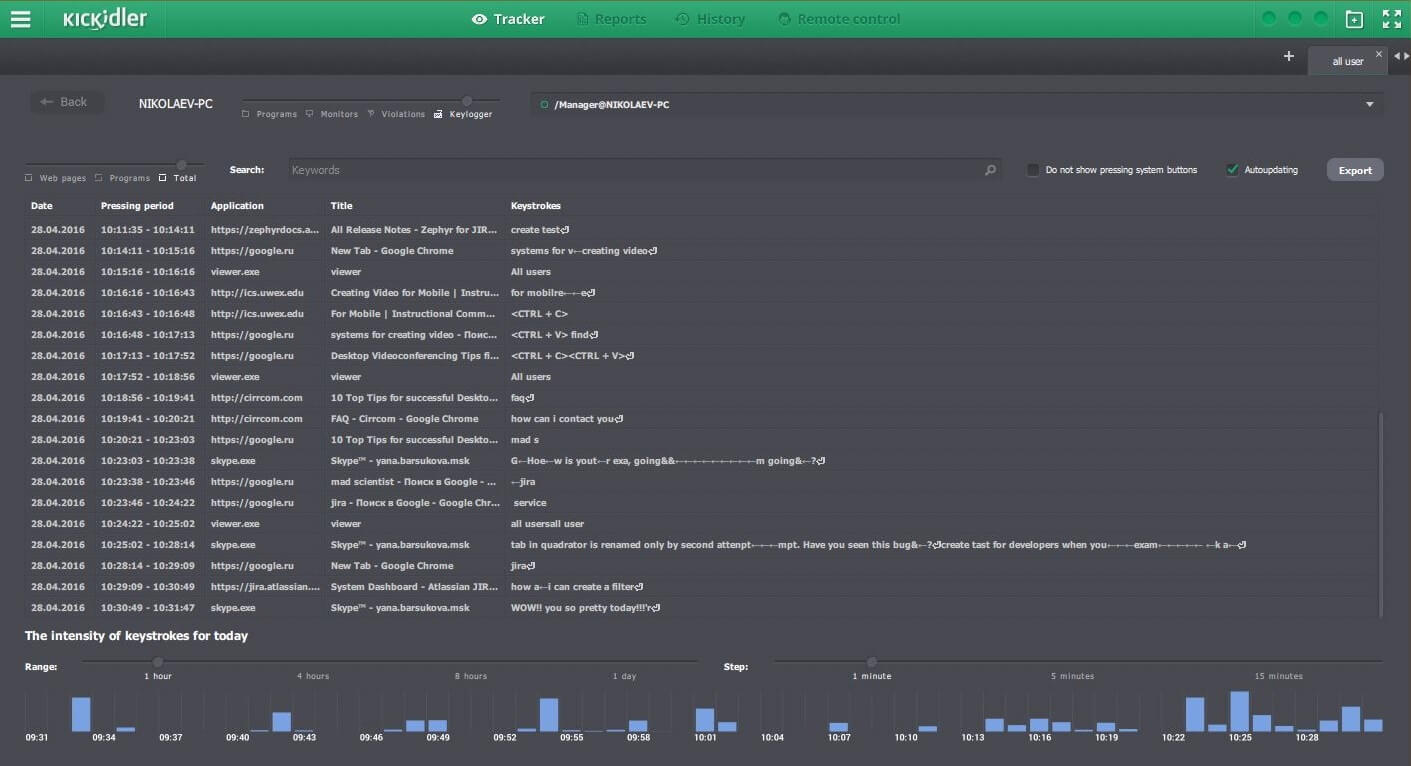
Screenshot: Keylogger tab in Viewer window
Computer remote control (PC administration via remote access)
Computer remote control feature provides solution for all basic tasks of remote PC administration, such as remote computer technical support, remote desktop control, etc. For instance, a system administrator may get remote access to an employee’s desktop and install applications this employee needs for work. This feature may be also useful for remote training, for example, when an employee located in a remote office needs training for working in some particular program.
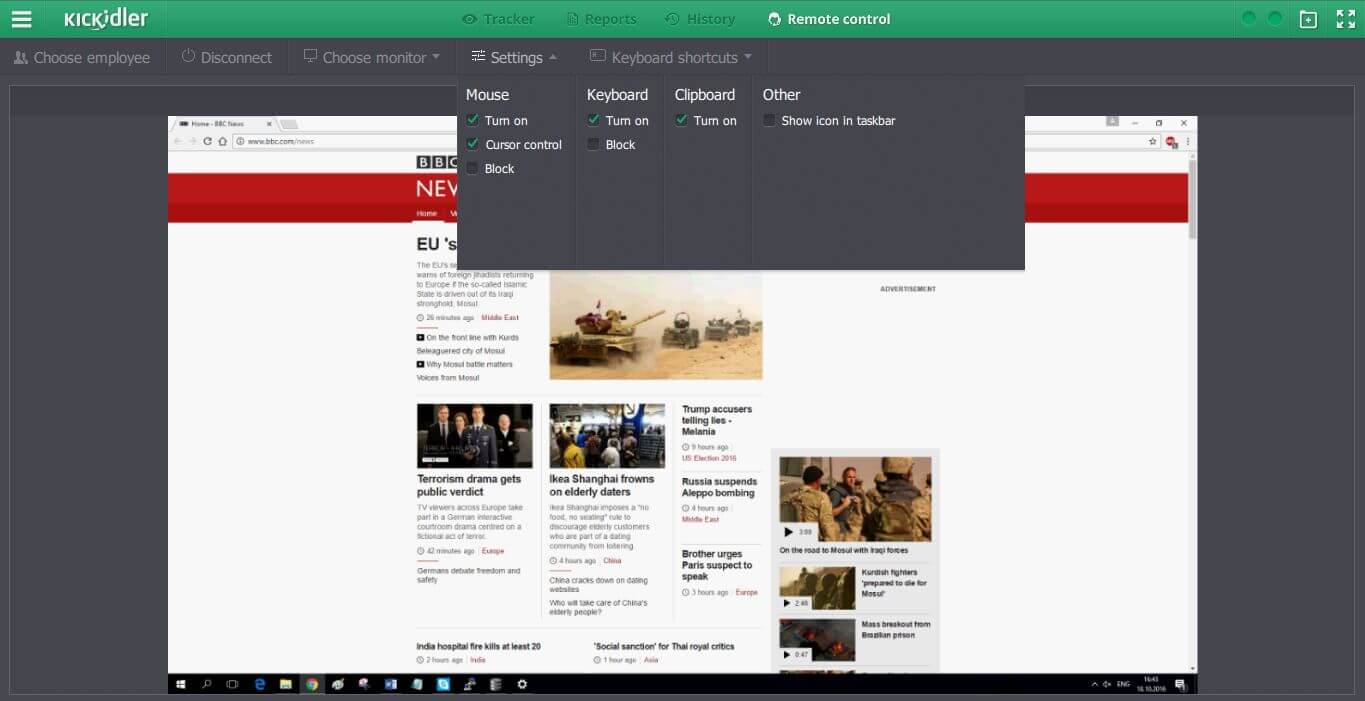
Screenshot: access to remote desktop with the use of Kickidler
Problems that Kickidler solves:
- assessment of overall productivity of employees, departments, heads of deaprtments, and the company itself;
- precise employee time-tracking;
- remote employee monitoring;
- detailed visual and technical monitoring of employee computer activities;
- lost corporate data recovery (e.g. logins and passwords);
- enhancement of information security, timely detection of insider threats;
- employee computer remote control.
We position Kickidler as a b2b product, though it does not mean it can’t be used for private purposes. For instance, it is a great tool for parental control on the home computer, for remote access to the desktop, for remote monitoring of personal computers – but only if the persons under monitoring are notified. Kickidler is also used at computer classes at schools.
Range of employee computer monitoring programs
Our company is certainly not the only employee monitoring software developer on the market. Among our competitors we should definitely name Teramind, HubStaff, ActivTrack, Time Doctor, Toggl, Skype Time, Activity Monitor.
We recommend to check the rating of monitoring software in order to compare their features and functional scope.
DLP Systems for Corporate Data Security Provision
Although spyware programs have many useful functions, they do not provide for in-depth network traffic analysis for data leaks prevention. So, that’s where DLP systems step onto the scene.
DLP systems, short for Data Leak Prevention systems, are powerful and expensive software solutions and true IT-security keystones in every sense of the word. DLP solutions may include computer time-tracking features as an option, but primarily they are not designed for simple employee computer monitoring. They are intended for complex inbound/outbound traffic analysis aimed at detection of any insider information leaks. That is, in other words, data traffic control.
The key DLP system developers of today are Symantec Corp., Verdasys Inc, Forcepoint (previously known as Websense), Intel Security and InfoWatch. Their client base mainly consists of international banks, public institutes, industrial and power enterprises all over the world.
DLP systems analyze data traffic using formal and content-based methods. The first one implies recognition of specific tags or labels the documents are marked with, and hash functions. Content analysis feature is monitoring all the scope of inbound/outbound traffic using a number of data filters. Combining these methods means a higher level of data security, but does not give 100% guaranteed protection. We recommend using both DLP system and employee monitoring software.

GPS-tracking Bracelets and Other Tracking Systems
Such devices are designed for GPS-tracking of the personnel at the employer’s premises. They allow to prevent unauthorized access of the employees with no with admittance permission to certain zones of the employer’s premises. Some employee monitoring programs, e.g. Hubstaff, provide for personnel GPS-tracking as an option.
GPS vehicle locators are installed onto corporate cars in order to track their location remotely. They help to prevent idling of corporate vehicles, breaches of work duties and negligent performance. Thus, some corporate driver will have to explain to the manager how come that while on a business trip he hit the hottest night spots of the city driving a corporate car.
Today many IT-companies introduce their GPS-tracking bracelets to the market. Among the most known GPS-tracking manufacturers we may mention NetcorpGPS of Australia.
All GPS-bracelets designed for corporate purposes are actually analogues of iconic GPS-tracking Kid SmartWatch created for parents to track their kids’ location in real-time. GPS-tracking data from these devices is sent to the central server, to the boss’s PC or smartphone.
Navigation solutions are often combined with an option of biometric scanners or access cards. But this is a much higher level of data security, which is used, for example, at military bases, nuclear plants, and other objects of strategic importance. In corporate companies which have nothing to do with strategic importance status, Boss Control system and those alike are installed. They are scanning the employees’ fingerprints on their entering and leaving the office for the purpose of check-in and check-out time records. Boss Control stands out of the crowd as its data processing center is located in the cloud.
Employee Monitoring = Better Productivity
Employee monitoring can be carried out in many different ways, and there is a lot of employee monitoring software to meet these needs. The current laws provide for the right of the employers to monitor their employees. So, it's up to employers to opt for free spying software or a powerful DLP system.
We recommend you taking a ‘test drive’ of Kickidler. You may download a free trial version so that you will be able to try all the features available for trial version for as long as 14 days, and not to buy a wrap-up product with no previous testing.
Some extra reference materials:
How the insider who was stealing the client base was found. Real case
Dynamics of Employee Activity: what is it and why is it important for the leader to monitor it
Control of school computer lessons using monitoring program Kickidler

Contents
Share this post